Differences between Computer Virus and Computer Worm
Contents
Comparison of computer viruses and computer worms[edit]
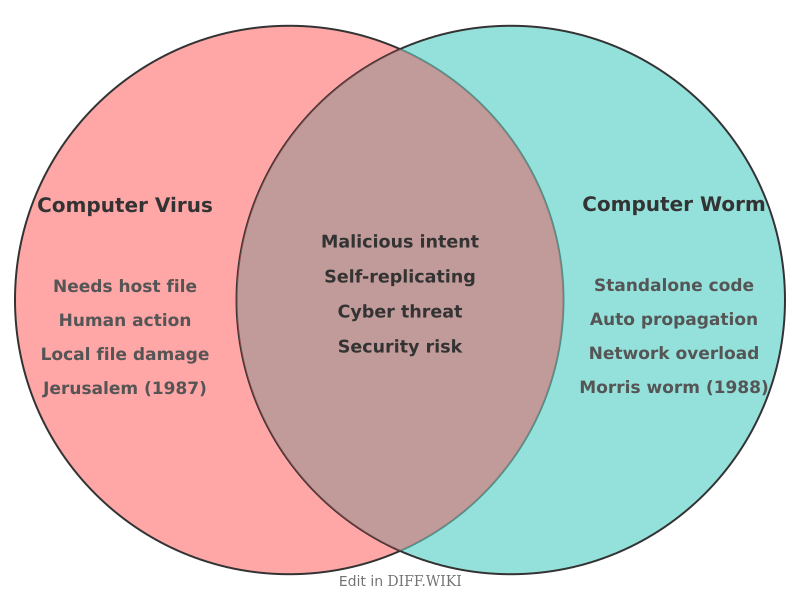
Computer viruses and computer worms are categories of malicious software (malware) designed to infect digital systems and replicate. While these terms are often used interchangeably in popular media, computer science definitions distinguish them based on their method of propagation and their dependency on host files. A virus requires a host program or human intervention to spread, whereas a worm functions as a standalone entity that moves through network connections independently.
Comparison of characteristics[edit]
| Category | Computer virus | Computer worm |
|---|---|---|
| **Host dependency** | Requires an existing file or program to attach to. | Independent standalone software. |
| **Propagation method** | Spreads through human actions like opening email attachments or sharing files. | Spreads automatically by exploiting network vulnerabilities. |
| **Replication speed** | Limited by the frequency of user interaction. | Rapid; can infect thousands of systems in minutes. |
| **Primary target** | Modifies or deletes local files and applications. | Consumes network bandwidth and system resources. |
| **Historical example** | Jerusalem (1987) | Morris worm (1988) |
| **Primary defense** | Antivirus software and file-level scanning. | Network firewalls and security patching. |
Functional distinctions[edit]
A computer virus operates by inserting its own code into a legitimate executable file or document. This process is referred to as infection. When a user executes the infected application, the viral code runs first, searching the local file system for other targets to corrupt. Because viruses rely on file sharing, they were the dominant form of malware during the era of physical media, such as floppy disks. Modern viruses often spread through "macro" code in office documents or infected installers downloaded from the internet.
Computer worms do not modify existing files. Instead, they exist as complete programs that seek out other computers on a network. A worm scans the network for machines running services with known security flaws. Once a vulnerability is identified, the worm sends a copy of itself to the target system. This cycle repeats without any input from the computer user. The primary damage caused by a worm is often the exhaustion of network bandwidth or the installation of "backdoors" that allow unauthorized remote access.
Historical context[edit]
The formal study of these programs began in the early 1980s. Researcher Fred Cohen defined a computer virus in 1983 as a program that can "infect" other programs by modifying them to include a version of itself. This definition emphasized the parasitic nature of the code.
The distinction became clearer in 1988 with the release of the Morris worm. Created by Robert Tappan Morris, this program was intended to gauge the size of the internet but contained a logic error that caused it to re-infect machines multiple times. This resulted in significant system slowdowns and crashes across the ARPANET. Unlike the viruses of that time, the Morris worm required no human assistance to move between university and government servers.
References[edit]
- Cohen, F. (1987). "Computer Viruses: Theory and Experiments". *Computers & Security*. 6 (1): 22–35.
- Denning, P. J. (1990). *Computers Under Attack: Intruders, Worms, and Viruses*. ACM Press.
- Nazario, J. (2004). *Defense and Detection Strategies against Internet Worms*. Artech House.
- Orman, H. (2003). "The Morris Worm: A Retrospective". *IEEE Security & Privacy*. 1 (5): 35–40.